
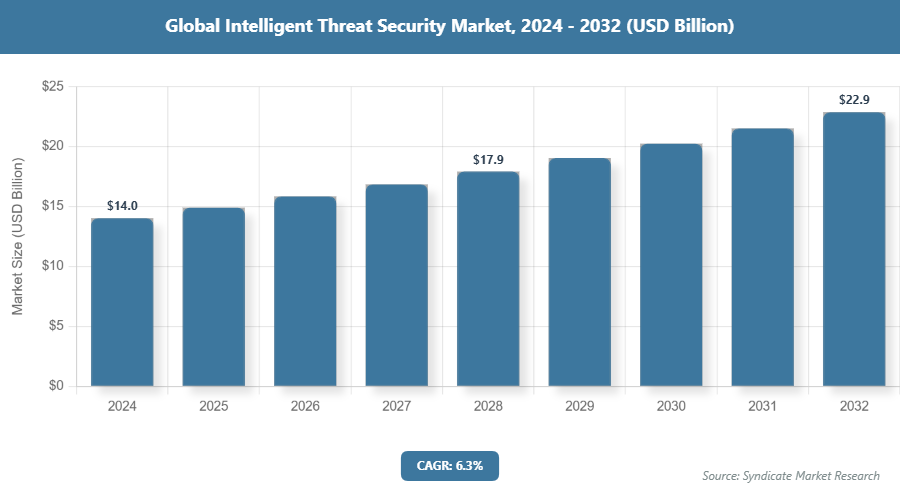
According to Syndicate Market Research, the global intelligent threat security market hit about USD 14.04 Billion in 2024. The intelligent threat security industry is set to reach around USD 14.92 Billion in 2025 and a whopping USD 22.90 Billion by 2032, growing at a steady compound annual growth rate (CAGR) of roughly 6.3% from 2026 to 2032. This all-encompassing study report conducts a granular, stepwise dissection of the market ecosystem, equipping stakeholders, investors, and sector insiders with priceless observations. Coverage spans a multitude of important variables, such as intelligent threat security market scale, fundamental drivers, surfacing trends, competitive pressures, and predictive scenarios.
Report Description
This report is a comprehensive study providing a detailed analysis of the intelligent threat security market. The report defines the type of intelligent threat security along with its applications in various industry verticals with reference to various regions and major countries. Further, the study has identified and studied all the major players operating in the global intelligent threat security market space and equated based on various parameters such as market revenue, annual sales volume, historical growth rate, and business strategies. Based on all these insights, the global intelligent threat security market report recommends a business strategy for the current market participants to strengthen their market positions. Moreover, the report also suggests a market entry strategy for the new market entrants.
Furthermore, the intelligent threat security market report has also identified the major vendors and distributors operating in all the major regions. This analysis and data is expected to help the market players to strengthen their market distribution channels and expand their geographical reach.
Intelligent Threat Security Market Strategic Analysis
The intelligent threat security market report has analyzed the market using various marketing tools such as Porter’s Five Forces Analysis, player positioning analysis, SWOT analysis, market share analysis, and value chain analysis. In Porter’s Five Forces analysis, the market dynamics and factors such as the threat of substitute for intelligent threat security, threat of new entrants in the intelligent threat security market, bargaining power of buyers, bargaining power of suppliers to intelligent threat security providing companies, and internal rivalry among the intelligent threat security providers are analyzed to provide the readers of the report with a detailed view of the market current dynamics.
This analysis helps the users of the report to evaluate the intelligent threat security market based on various parameters such as economies of scale, switching costs, brand loyalty, existing distribution channels, capital investments, manufacturing rights & patents, government regulations, the impact of advertisements, and impact of consumer’s preferences. This all summarized data is anticipated to help the key decision-makers of the industry in the decision-making process. Further, this analysis also answers the imperative question for new entrants to enter the intelligent threat security market or not.
Intelligent Threat Security Market Key Trends Analysis
The report has analyzed the major factors which are impacting the growth of intelligent threat security market. Driving factors that are positively impacting the demand for intelligent threat security and restraining factors that are hindering the growth of intelligent threat security market are discussed in detail along with their impacts on the global intelligent threat security market. Further, the trends which are shaping the market and impacting the growth of the market are identified and discussed in detail in the reported study. Moreover, other qualitative factors such as risks associated with the operations and major challenges faced by the players in the market space are included in the report.
Intelligent Threat Security Market Key Segment Analysis
The study provides a decisive view on the intelligent threat security by segmenting the market based on type, applications, and region. All the segments of the intelligent threat security market have been analyzed based on present and future trends. The data for the market and its segments are forecast for 2024 to 2030. The report has identified the segments contributing most to the overall market growth in terms of revenue along with the factors boosting their growth.
Based on type, the global intelligent threat security market is segmented into Log Management, Security Information and Event Management, Risk Management, Identity and Access Management. Detailed qualitative as well as quantitative type segment analysis will be provided in the report for 2018 to 2030.
Based on applications market is segmented into Healthcare, BFSI, IT & Telecommunication, Manufacturing, Defense, Others. Various potential opportunities and factors affecting the different applications are analyzed and included in the report study.
Intelligent Threat Security Market Regional Trends and Market Player’s Analysis
Regionally, the market is divided into North America, Europe, Asia Pacific, Latin America and Middle East and Africa. Wherein, North America dominated the global intelligent threat security market in 2023. Over the forecast period, the Asia Pacific region is anticipated to witness the highest CAGR for the intelligent threat security market.
Intelligent Threat Security Market Size By Region

Get more information about this report - Request Free Sample Copy
Major companies holding significant market shares in the global intelligent threat security market are analyzed considering their market revenue, market shares, business strategies, recent developments, and growth rates. Recent events for these companies such as new solution/product launches, research initiatives, acquisitions, geographical expansions, and technological advancements are considered in finalizing their position in the intelligent threat security market player positioning. The information provided in the intelligent threat security market research study is expected to be helpful for all the key stakeholders of the intelligent threat security value chain and technology ecosystem.
The report provides company market share analysis in order to give a broader overview of the key players in the intelligent threat security market. Major players in the global intelligent threat security market are Cyveillance (U.S.), Dell Secureworks (U.S.), IBM (U.S.), Intel Security (U.S.), Juniper Networks (U.S.), Symantec (U.S.), Trend Micro (Japan), Webroot (U.S.), BAE Systems Plc (U.K.), FireEye Inc (U.S.), among others.
| Report Attributes | Report Details |
|---|---|
| Report Name | Intelligent Threat Security Market |
| Market Size in 2024 | USD 14.04 Billion |
| Market Size in 2025 | USD 14.92 Billion |
| Market Forecast in 2032 | USD 22.90 Billion |
| Growth Rate (2026-2032) | CAGR of 6.3% |
| Base Year | 2025 |
| Historical Year | 2020 - 2025 |
| Forecast Year | 2026 - 2032 |
| Number of Pages | 282 |
| Report Coverage | Revenue Forecast, Market Dynamics, Company Profile, Competitive Landscape, Recent Developments, Growth Factors, and Recent Trends |
| Key Companies Covered | Cyveillance (U.S.), Dell Secureworks (U.S.), IBM (U.S.), Intel Security (U.S.), Juniper Networks (U.S.), Symantec (U.S.), Trend Micro (Japan), Webroot (U.S.), BAE Systems Plc (U.K.), FireEye Inc (U.S.) |
| Segments Covered | By Type, By Applications, and By Region |
| Regions Covered | North America, Europe, Asia Pacific (APAC), Latin America, Middle East and Africa (MEA) |
| Customization Scope | Customization for Segments, Region, Country-level will be provided. Avail customized purchase options to meet your exact research needs. Request For Customization |
Major Highlights of the Intelligent Threat Security Market report study:
The report segment of the global intelligent threat security market as follows:
Global Intelligent Threat Security Market: By Type
The report study is drafted to provide actionable insights to the following mentioned audience:
These players adopted different strategies so as to hold major market share in this market. Some of the major players in Intelligent Threat Security industry includes.
Based on the Intelligent Threat Security market analysis, North America is predicted to held the highest share in the Intelligent Threat Security market during the forecast period.
The statistical data of the top market players of Intelligent Threat Security industry can be obtained from the company profile section specified in the report. This section incorporates analysis of top player’s operating in the Intelligent Threat Security industry as well as their last five-year revenue, segmental revenue, product offerings, key strategies adopted, and geographical revenue produced.
The study offers a decisive view on the Intelligent Threat Security by segmenting the market based on Type, Applications, and region.
The report gives a nitty-gritty assessment of the market by featuring data on various viewpoints that incorporate drivers, restraints, opportunities, and threats. This data can assist stakeholders in making suitable decisions before investing.
The sample for Intelligent Threat Security market report can be received on-demand from the website as and when required.Direct call services or 24*7 chat support are provided to procure the sample report.
List of Figures
List of Tables
1.1 Research Methodology
The process of market research at Syndicate Market Research is an iterative in nature and usually follows following path. Information from secondary is used to build data models, further the results obtained from data models are validated from primary participants. Then cycle repeats where, according to inputs from primary participants, additional secondary research is done and new information is again incorporated into data model. The process continues till desired level of information is not generated.
To calculate the market size, the report considers the revenue generated from the sales of the market providers. The revenue generated from the sales of market is calculated through primary and secondary research. The key players operating in the market across the globe are identified through secondary research and a corresponding detailed analysis of the top vendors in the market is done. The market size calculation also includes clinical trial phase segmentation determined using secondary sources and verified through primary sources.
1.2 Secondary Research
The secondary research sources that are typically referred to include, but are not limited to:
The sources for secondary research includes but is not limited to: Factiva, Hoovers and Statista

1.3 Primary Research
We conduct primary interviews on an ongoing basis with industry participants and commentators in order to validate data and analysis. A typical research interview fulfills the following functions:
The participants who typically take part in such a process include, but are not limited to:
1.4 Models
Where no hard data is available, we use modeling and estimates in order to produce comprehensive data sets. A rigorous methodology is adopted in which the available hard data is cross referenced with the following data types to produce estimates:
Data is then cross checked by the expert panel.
1.4.1 Company Share Analysis Model
Company share analysis is used to derive the size of global market. As well as study of revenues of companies for last three to five years also provide the base for forecasting the market size and its growth rate. This model is built in following steps:

1.4.2 Revenue Based Modeling
Revenue based models can be built in two ways - Top-Down or Bottom-Up irrespective of industry. Market size estimated from company share analysis acts as a validation point for bottom-up approach where as it acts as starting point for top-down approach.

1.5 Research Limitations
Inflation is not a part of pricing in this report. Prices of the products and its derivatives vary in each region and hence similar revenue ratio does not follow for each individual region. The same price for each type has been taken into account while estimating and forecasting market revenue on a global basis. Regional average price has been considered while breaking down this market by end user in each region.
We focus on the quality and accuracy of the report
Our expert team will assist with all your research needs and customize the report
Get you queries resolved from our expert analysts before and after purchasing the report
Instant delivery in the form of a PDF/PPT/Word Doc to your email address, within 12 hours after receiving the full payment.
Analysts will provide deep insights about the reports
* We value your privacy and will never rent or sell your email address.

Comprehensive & Focused Market Reports Large Archive of Excellent Market and Industry Analysis Reports that Deliver Business Intelligence.

Safe & Secure Payment Solutions
Enabled by SSL, we provide you numerous safe payment options for
risk-free transactions.

Superior Customer Experience We serve our
customers through calls, emails and live chats for 365 days, 24x7.